by Cody Dumont
October 8, 2020
Exploitable vulnerabilities create gaps in the network's integrity, which attackers can take advantage of to gain access to the network. Once inside the network, an attacker can perform malicious attacks, steal sensitive data, and cause significant damage to critical systems. By identifying the most at-risk vulnerabilities, analysts and security teams can better focus patch management efforts and better protect the network, thereby reducing the organization’s Cyber Exposure gap. To effectively mitigate vulnerabilities on a network, a security team must be aware of the current exploitable vulnerabilities. The Common Vulnerability Scoring System (CVSS) is a method to define and characterize the severity of a vulnerability. In addition to specifying the severity of a vulnerability, Nessus also tracks the exploitability of a vulnerability based on information located in several publicly-known exploit repositories. This report provides a summary of the most prevalent exploitable vulnerabilities.
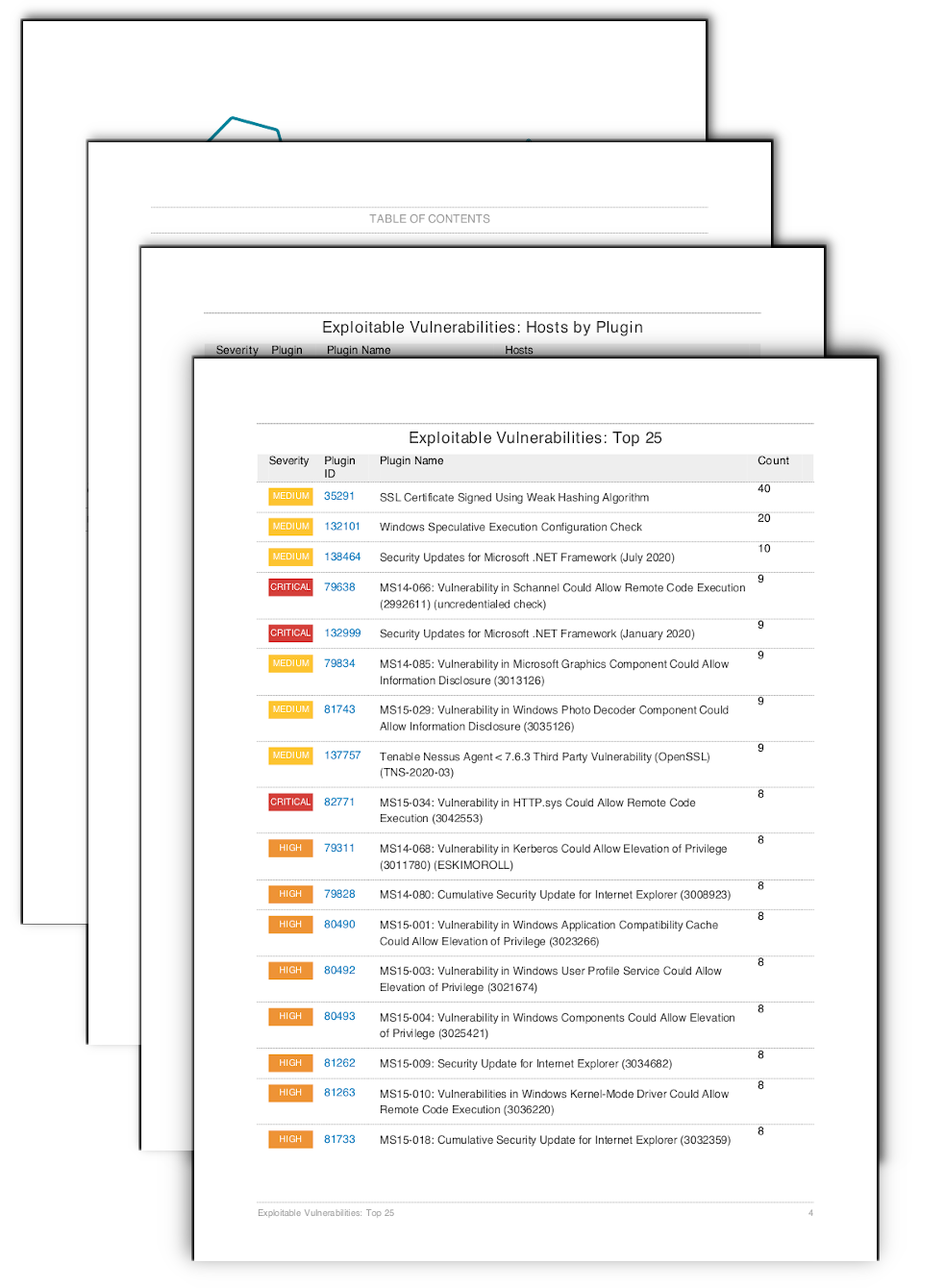
Nessus identifies exploitable vulnerabilities present in your scan results. The report contains two tables which bring focus to the exploitable vulnerabilities. The first table provides a summary view of the top 25 most exploitable vulnerabilities based on the host count. The following table provides a list of vulnerabilities and the associated hosts, which allows the security and IT operations teams to work together to create an effective mitigation plan. The report is also beneficial to executives to tie the risk mitigation efforts to business initiatives.
This report provides information on exploitable vulnerabilities that have been detected on the network and utilizes other data attributes such as the CVSS base score and information from exploit frameworks such as Core Impact, Canvas, and several others, to accurately represent and communicate cyber risk to the business unit. The cumulative view of the data provided by this report, assists the analyst with a comprehensive understanding of the discovered critical and exploitable vulnerabilities. Using various visual aids, the report displays the data in an easy to understand manner. The information from this report will enable analysts to discover assets, measure the attack surface, prioritize, and remediate critical and exploitable vulnerabilities in a timely manner.
Chapters
The Exploitable Vulnerabilities: Top 25 table uses the plugin attribute “exploit_available” to identify software that have working exploits in the wild. The data is then sorted by the count, or number of affected hosts. While some plugins may be present more than one time on a single host, for the most part a plugin will only be present once on each host. Exploitable vulnerabilities expose the organization to many different attack frameworks and script kiddie attacks. These vulnerabilities should be prioritized and the software removed or updated to a supported version as soon as possible.
The Exploitable Vulnerabilities: Hosts by Plugin table provides the IT operations team with an action plan and the identified hosts for each vulnerability. The IT managers are able to use this information in planning patch deployments and work with the information security team in risk mitigation efforts. The table also identifies exploitable software and then sorts the scan results using the severity and plugin ID. The entries in the Hosts column are then sorted in ascending order.