by Josef Weiss
The Cyber Essentials is a UK government-backed framework which is designed to assist organisations in protecting themselves against common threats. The Cyber Essentials provides a basic cyber security foundation that can serve as a stepping stone to a more comprehensive zero-trust approach. The Cyber Essentials is built on 5 key components that, when implemented correctly, can reduce cyber risk. The five key components are:
- Firewalls and Boundary Devices
- Secure Configurations
- Access Control
- Malware Protection
- Patch Management
Tenable has released a series of reports, that focuses on each of the five basic technical controls, which organisations can use to help strengthen their defences against the most common cyber threats.
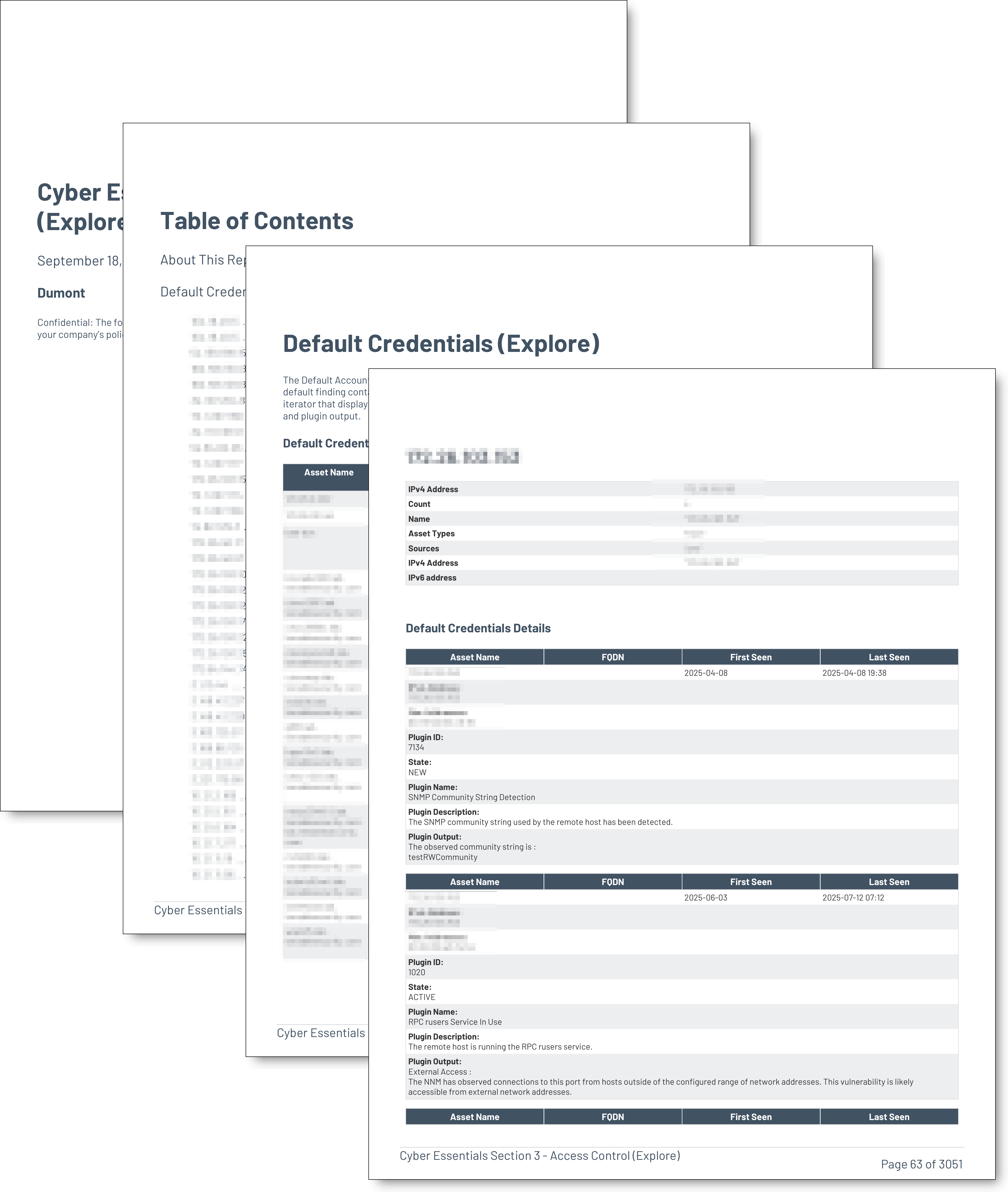
The focus of this report is Section 3 - Access Control. This key requirement supports the goal of reducing an organisation’s risk from the most common cyber threats. The Cyber Essentials focuses on preventing high impact attacks, such as phishing, malware infection, and unauthorized access. Strong access control can limit the number of accounts which attackers can compromise, ensuring that individuals only have access which is required to perform job functions.
This key component applies to all the following in scope devices: Boundary Firewalls, Desktop Computers, Laptops, Routers, Servers, Iaas, PaaS, and SaaS devices.
This report contains the following chapters:
Default Accounts - The Default Accounts chapter contains a summary table displaying the assets which have a findings result which contains a default finding containing the keywords (credential, account, password, user, or community). This summary is followed by an iterator that displays the detailed findings. Included in the detailed findings are host details, along with the plugin description and plugin output.
Account Management - CSCv8 - This chapter provides organisations with information which specifically measures against the compliance standard related to CSCv8, related to Account Management. The CSC is a widespread framework used globally to assist organizations improve their cyber security posture.
Windows User Account Information - This chapter contains the Windows User Account plugin summary chart which displays the plugin counts sorted by the number of plugins detected. The chart is followed by details for each asset where the plugin is detected
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success