by Josef Weiss
The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides technical and operational requirements for organizations accepting or processing payment transactions. The guidance also applies to software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 4.x. Any organization that handles payment card information must comply with the PCI DSS and must demonstrate compliance annually. Tenable Vulnerability Management is able to help organizations monitor ongoing PCI DSS compliance.
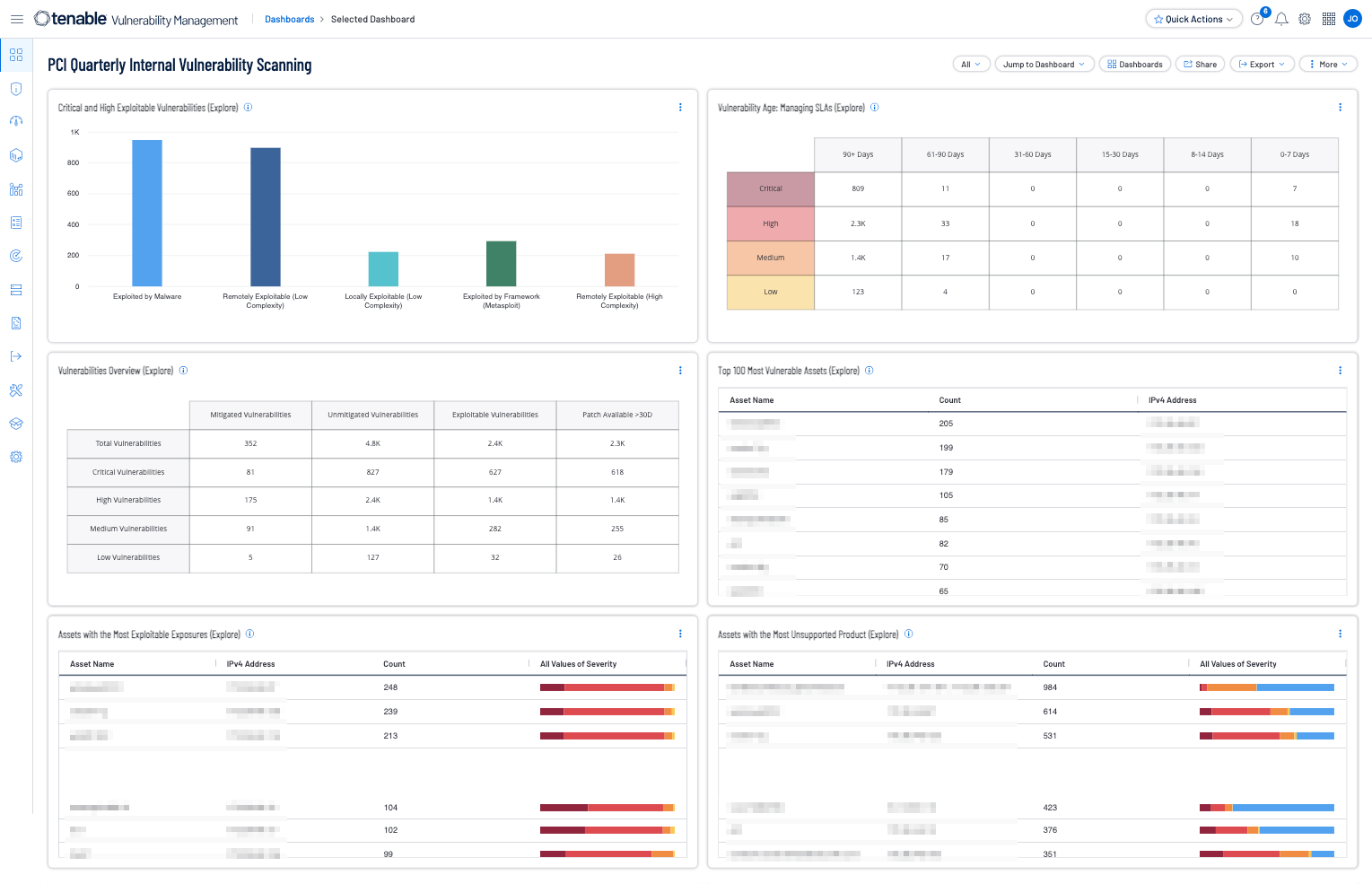
The PCI Quarterly Internal Vulnerability Scanning dashboard presents extensive data about the vulnerability status of the network based on the available data. The dashboard can be used to gain insight into all vulnerability results, or it can be modified to focus exclusively on the results related to the cardholder data environment (CDE). Organizations can configure repositories or asset lists in order to tailor the focus of the dashboard. When the dashboard is added from the Tenable.sc Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the dashboard will update all filters in the components. Security teams can use this dashboard to identify and monitor vulnerability remediations across the organization.
Vulnerability-related components in this dashboard are filtered for high and critical severity vulnerabilities in order to focus on vulnerabilities of particular concern to PCI internal network scans. Identified vulnerabilities are tracked by time, severity, and host in order to provide multiple perspectives into the vulnerability status of the organization. By adding asset lists or repository filters, organizations can tailor the dashboard to only use data specifically related to internal vulnerability scanning requirements (PCI DSS Requirement 11.3). Different views of the vulnerability data provide a comprehensive view of the vulnerability status of the CDE or organization. Organizations can assess their level of adherence with PCI requirements focusing on vulnerabilities within the organization. The components in this dashboard are focused on PCI requirement Requirement 11.3, which specifically addresses the need to perform quarterly internal vulnerability scans and rescans as needed.
Tenable provides several solutions for organizations to better understand vulnerability management. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management (formerly Tenable.io) discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirements for this report are: Tenable Vulnerability Management.
Widgets:
- Critical and High Exploitable Vulnerabilities (Explore) - This widget focuses on the most severe current threats, critical and high exploitable vulnerabilities to help prioritize remediation.
- Vulnerability Age: Managing SLAs (Explore) - This widget provides a view of vulnerabilities based on severity and age.
- Vulnerabilities Overview (Explore) - This widget assists in tracking vulnerability mitigations. The matrix presents vulnerability summary information by severity.
- Top 100 Most Vulnerable Assets (Explore) - This table presents a list of the top most vulnerable assets at risk for exploitation. Information is filtered by vulnerabilities of high or critical severity that are exploitable, and is sorted by total vulnerabilities.
- Assets with the Most Exploitable Exposures (Explore) - This widget displays the assets that have the most vulnerabilities that are exploitable by any method.
- Assets with the Most Unsupported Product (Explore) - This widget displays the assets that currently have the highest count of unsupported products in the environment.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success