by Megan Daudelin
October 6, 2015
Detecting the various operating systems on a network can be a daunting task. Understanding which operating systems connect to the network can improve a security team’s ability to mitigate vulnerabilities and secure the network. Identifying the most common operating systems on a network is essential to an effective security program. By leveraging the capabilities of Tenable.sc and the Nessus Network Monitor (NNM), security teams can easily identify operating systems on a network and tailor their mitigation efforts accordingly.
The Passive OS Detection report assists security teams in identifying the operating systems that are present on the network so that security initiatives can be more focused. Passive OS detections from the NNM plugin “Operating System Fingerprint” (ID 1) are used to gather the data presented in this report. Passive vulnerabilities are filtered by vulnerability text in order to detect the major operating system groups. This report provides an overview of the passively detected operating systems on an organization’s network.
The chapters in this report provide several views of the operating systems detected by NNM on the network. Components use filters for time, vulnerability text, and plugin type in order to provide the most accurate overview of operating systems that have connected to the network. Security teams can monitor the presence of operating systems by count and ratio over time to ensure that security efforts are focused on addressing the most relevant concerns.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Monitoring. The report requirements are:
- Tenable.sc 4.8.2
- NNM 5.9.0
- This report requires “Full Text Search” to be enabled for each analyzed repository.
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. The Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. By integrating with NNM, Tenable.sc CV’s continuous network monitoring is able to detect operating systems, applications, software, and events across the enterprise.
This report contains the following chapters:
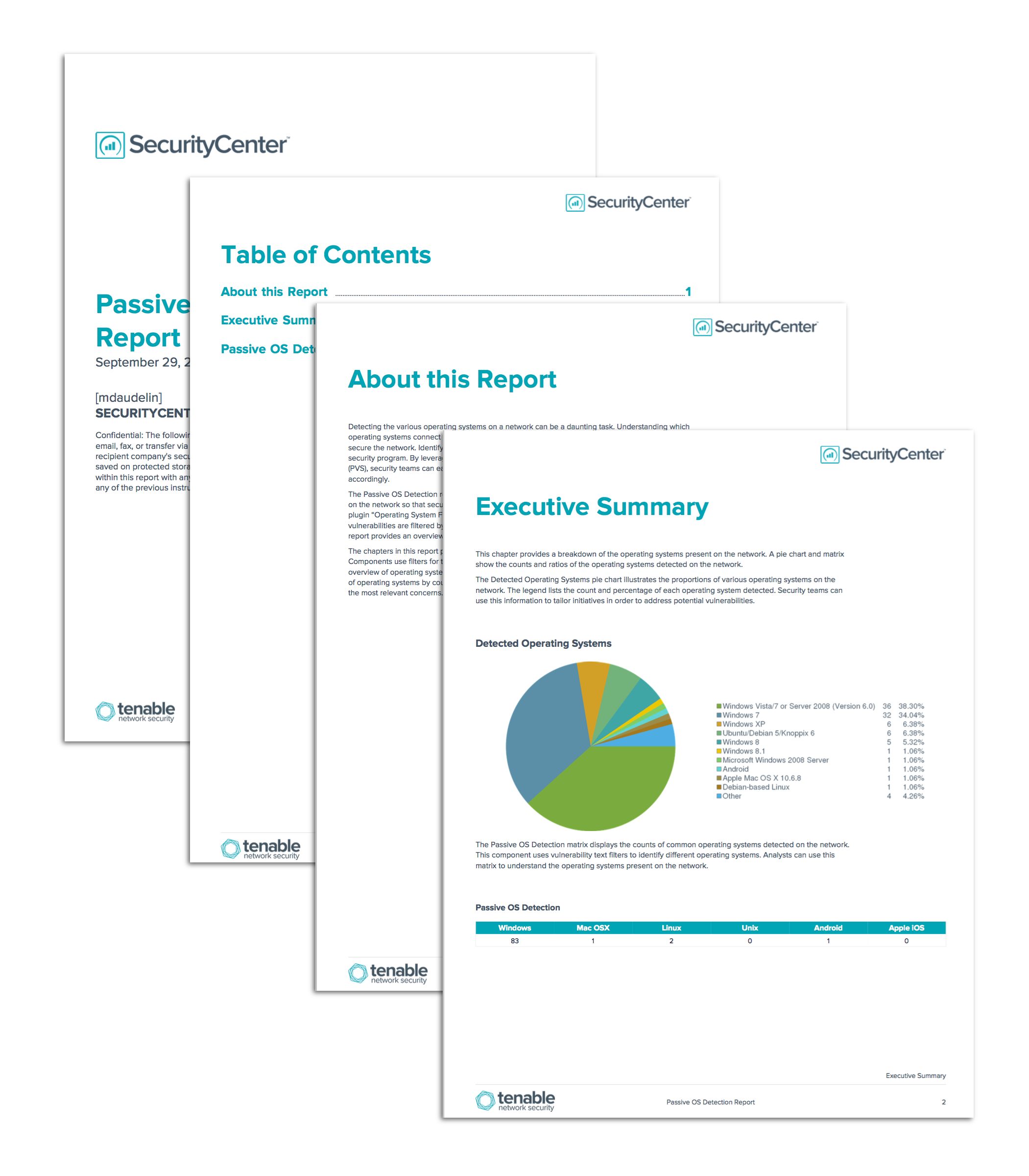
- Executive Summary: This chapter provides a breakdown of the operating systems present on the network. A pie chart and matrix show the counts and ratios of the operating systems detected on the network.
- Passive OS Detection: This chapter presents detailed information about the operating systems detected on the network. The components rely on detections from the Nessus Network Monitor (NNM) and filter the detections based on various characteristics.