by Josef Weiss
With of the increase in loss or unauthorized exposure of sensitive data, database security is a growing concern. Databases can contain valuable and sensitive data, making them a key target for cyber attacks. This Assurance Report Card or ARC assists in identifying weaknesses and compliance issues from the most common database vulnerabilities.
Physical devices such as firewalls and intrusion detection systems typically protect databases. While these controls are valuable, security of the database itself is becoming more critical as networks are becoming larger and more open, giving wider access to end users and clients. Database patching along with access control, authentication, and management are complimentary approaches to database security.
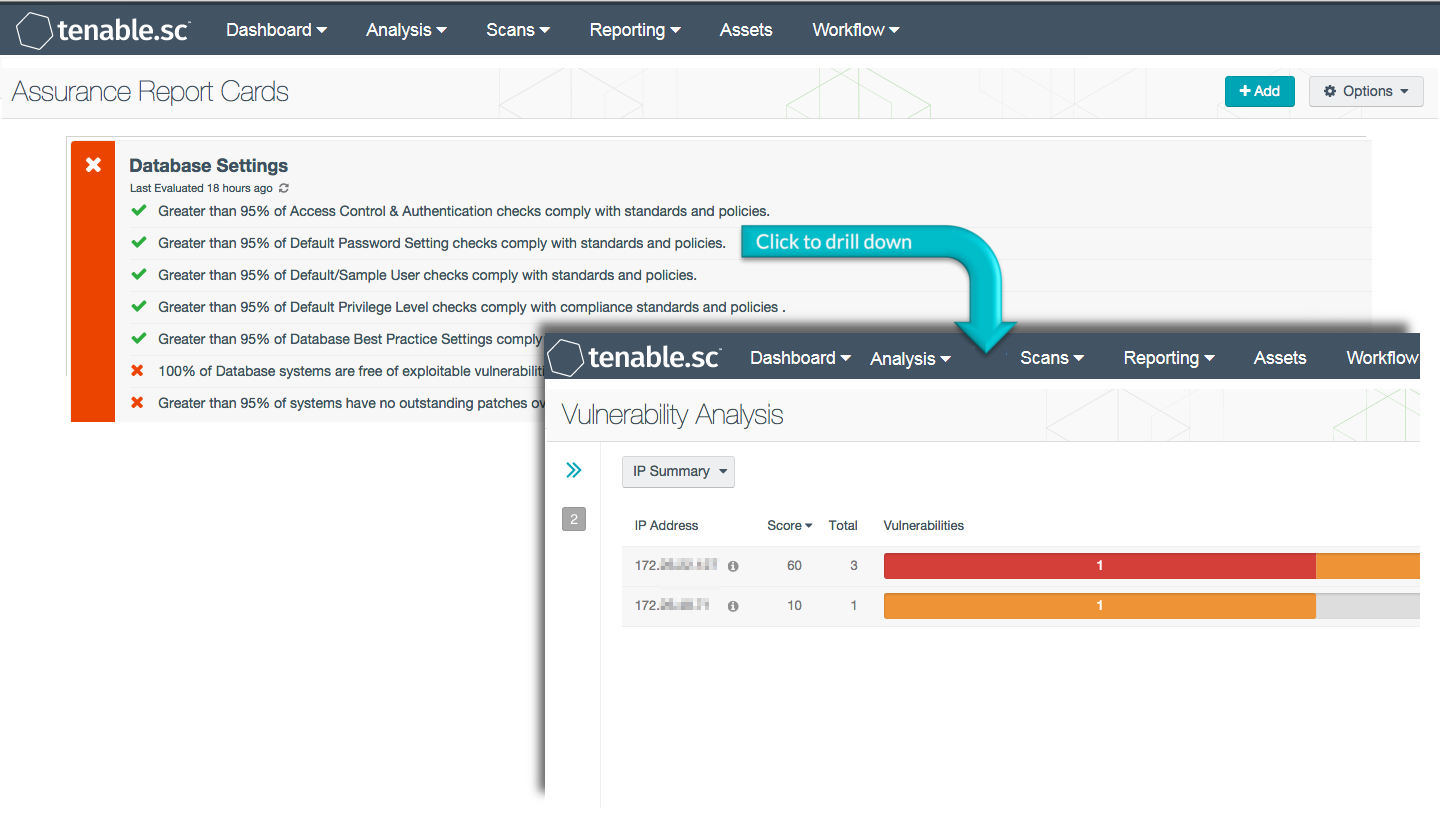
The Database ARC presents a series of policy statements that measure percentage compliance against organizational policies such as authentication policy, privilege policy, and best practices. These policies all share a common theme in assessing database compliance and configuration. Organizational policy should in turn be based on appropriate currently accepted standards.
The ARC and the associated policy statements rely on audit results received from Nessus scans utilizing database audit files for compliance scanning. The audit files and policy statements are guides that can be customized to fit the specific policy guidelines of the organization.
The policy statements within the ARC report on several of the key items from Tenable’s Five Critical Cyber Controls. Specifically these are: Removing vulnerabilities and misconfigurations, authorize users, and deploying a secure network. For additional information on Tenable’s Five Critical Cyber Controls visit http://www.tenable.com/blog/tenable-s-critical-cyber-controls-for-secure-systems
By reviewing the ARC, Compliance Managers can easily and quickly identify compliance concerns within database-driven systems based around these controls, and rapidly identify gaps in the database security programs or policies.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The ARC can be easily located in the Feed by selecting category compliance. The ARC requirements are:
- Tenable.sc 5.0
- Audit results
Tenable's Tenable.sc Continuous View (Tenable.sc CV) is the market-defining continuous network monitoring platform. Tenable.sc CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable's Nessus Network Monitor (NNM), as well as log correlation with Tenable's Log Correlation Engine (LCE). Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its network, in order to best measure compliance against complex standards.
The Database ARC contains the following policy statements:
- Greater than or equal to 95% of Access Control & Authentication checks comply with standards and policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on login restrictions have passed. This policy reports security concerns with database accounts, account configurations, and authentication parameters. The drill down filters display details on non-compliant results.
- Greater than or equal to 95% of Default Password Setting checks comply with standards and policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on default password restrictions have passed. A default password left in database environments is a potential security concern. This policy statement reports on the settings of default passwords in audited databases. The drill down filters display details on non-compliant results.
- Greater than or equal to 95% of Patch Management and Compliance checks comply with standards and policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on patch management and compliance checks have passed. Database patching can be one of the most effective solutions for securing a database and this policy provides a status on the organizational database patching effort. The drill down filters display details of non-compliant results.
- Greater than or equal to 95% of Default/Sample User checks comply with standards and policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on default/sample user compliance checks have passed. A default or sample user left in database environments is a potential security concern. This policy statement reports on the settings of default passwords in audited databases. The drill down filters display details of non-compliant results.
- Greater than or equal to 95% of Default Privilege Level checks comply with compliance standards and policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on default privilege level compliance checks have passed. Default privilege levels left in database environments is a potential security concern. This policy statement reports on the settings of default privilege levels in audited databases. The drill down filters display details of non-compliant results.
- Greater than or equal to 95% of Database Best Practice Settings comply with known best practice policies. This policy statement displays Compliant in green if at least 95% of the compliance checks on database best practices have passed. The best practice settings are defined in the Tenable Database Audit Files. Database settings that do not meet the settings are reported as compliance failures. The drill down filters display details of non-compliant results.
- 100% of Database systems are free of exploitable vulnerabilities. This policy statement displays Compliant in green if 100% of the database systems do not report an exploitable vulnerability. Exploits are typically publicly known published exploits and are easily available. In many cases, the vulnerability details will include information on what products can take advantage of any exploits, such as Metasploit or Core Impact. Initial settings are 100% as existing exploits typically have the highest priority item to resolve in any environment, and present the greatest potential threat to the enterprise.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success