Underminer Exploit Kit: How Tenable Can Help

The “Underminer” exploit kit is having widespread impact in Asian countries, particularly Japan. Thankfully, mitigation is relatively simple and involves patching and other well-known security best practices.
Contrary to popular belief, the exploit kit is not dead yet. “Underminer,” an exploit kit named and discovered by Trend Micro, is having widespread impact in Asian countries, particularly Japan. Its nefarious bootkit affects the system’s boot sectors and delivers the coin mining payload named Hidden Mellifera.
While the continued decline of Adobe Flash has led to a reduction in the prevalence of Exploit Kits, enterprises need to remember this attack vector remains a real problem. Underminer is quite sophisticated and has many of the capabilities utilized by other problematic exploit kits, including user-agent/browser profiling to determine Flash Player version and cookie detection to prevent repeated exploit site visits. In addition, RSA encryption of traffic is utilized prior to exploitation.
The following diagram from Trend Micro provides a useful high-level view of the stages and vectors of Underminer:
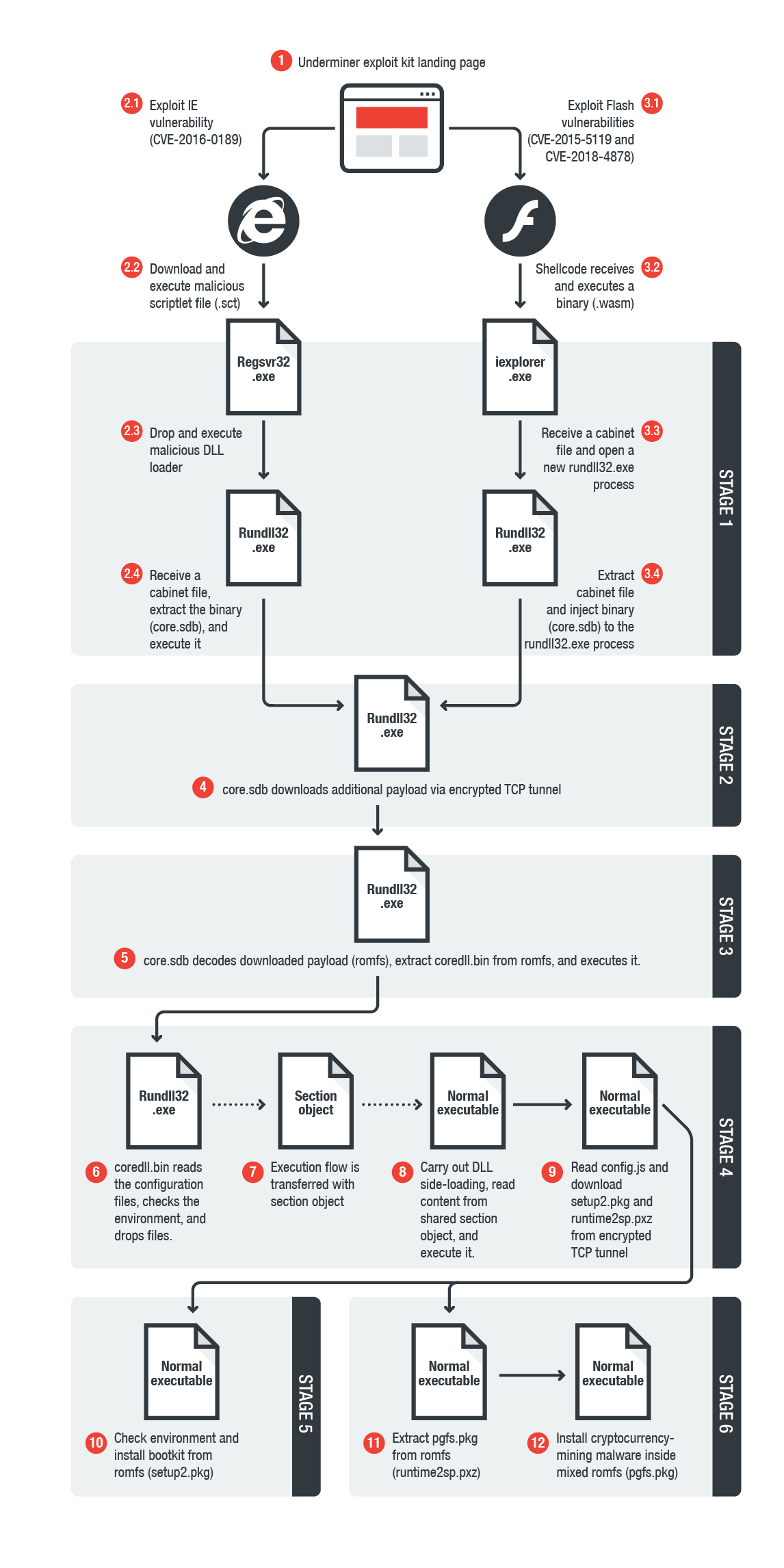
Source: Trend Micro, https://blog.trendmicro.com/trendlabs-security-intelligence/files/2018/07/underminer-exploit-kit-4.png.
As of 4:45 am EDT on July 27, the antivirus (AV) programs tested by VirusTotal have very limited coverage of the provided SHA-256 checksums (3/40). However, that’s bound to change with time and is likely due to the localized exploitation. Thankfully, mitigation is relatively simple and involves patching and other well-known security best practices, such as preventing unnecessary browser plugins, good firewall hygiene, antivirus updates, user awareness and so on.
Antivirus programs tested by VirusTotal
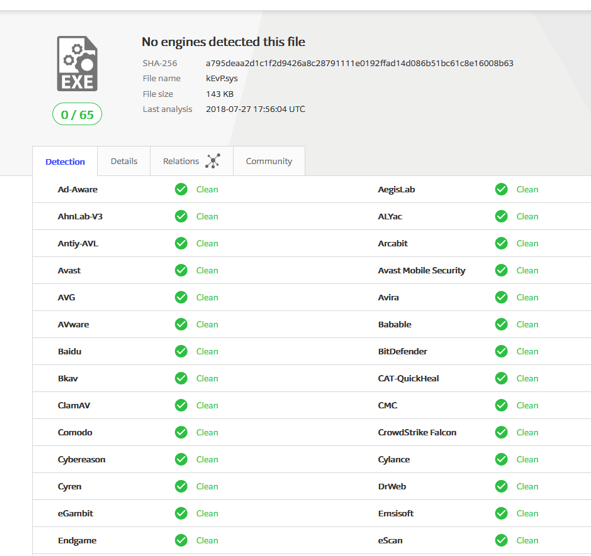
Source: VirusTotal, https://www.virustotal.com/#/file/a795deaa2d1c1f2d9426a8c28791111e0192ffad14d086b51bc61c8e16008b63/detection.
Tenable’s Coverage for Underminer Exploit Kit
|
CVE |
Plugin ID |
Description |
|
CVE-2015-5119 |
Adobe AIR = 18.0.0.144 Multiple Vulnerabilities (APSB15-16) |
|
|
CVE-2015-5119 |
Adobe Flash Player = 18.0.0.194 Multiple Vulnerabilities (APSB15-16) |
|
|
CVE-2015-5119 |
Google Chrome 43.0.2357.132 Multiple Vulnerabilities |
|
|
CVE-2015-5119 |
MS KB3065823: Update for Vulnerabilities in Adobe Flash Player in Internet Explorer |
|
|
CVE-2016-0189 |
MS16-051: Cumulative Security Update for Internet Explorer (3155533) |
|
|
CVE-2016-0189 |
MS16-053: Cumulative Security Update for JScript and VBScript (3156764) |
|
|
CVE-2018-4878 |
Adobe Flash Player = 28.0.0.137 Use-after-free Remote Code Execution (APSA18-01) (APSB18-03) |
|
|
CVE-2018-4878 |
KB4074595: Security update for Adobe Flash Player (February 2018) |
Additional Information:
Learn more about Tenable.io, the first Cyber Exposure platform for holistic management of your modern attack surface. Get a free 60-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

