Threat Hunting 101: Taming Your Data

Security teams around the world are struggling to keep up with the rapidly changing threat environment, while facing the pressure of being responsible for any malicious activity that happens on their watch. With so many moving pieces, it’s impossible to identify what threats are impacting your environment without making sure your foundations are covered.
The most basic foundation is visibility.
What should I be watching?
What do you need to watch? It depends on your environment. Effectively, you need to watch:
|
Data |
To answer the question... |
|
Network activity |
What is talking? |
|
Host/node activity |
What are devices doing? |
|
User authentication and access |
How are users interacting with devices? |
|
Security control activity |
How is security working? |
There are thousands of ways to collect data in these four categories. They make up the backbone of a comprehensive security monitoring program and ensure that you have complete visibility when something happens. This foundation is essential to finding the breadcrumbs left by an adversary.
When planning your monitoring, it helps to think “What is the worst thing that could happen?” or alternatively “What could get me fired?” and “How would I see that with my tools?” Those major concerns that you and your management have are valid; they tend to point toward the most important areas to protect. It’s our job as security professionals to ensure that there are sensors that collect information at any necessary point for visibility into these scenarios to recreate what happened.
Once you’re collecting data, it's easy to be overwhelmed. Unfortunately, an abundance of data is a sign that you’re doing something right. It also gives security tools a chance to understand what is normal.
Too much data and not enough time...
Once the data is there, it's time to tame it so that its usable. A giant pile of unusable data doesn’t provide value to anyone.
First off, group things that are similar for analysis. This helps to limit your scope, not by limiting the data, but by creating profiles for different kinds of devices and activities that are common in your environment.
You can start with device identification, just to see what’s out there:
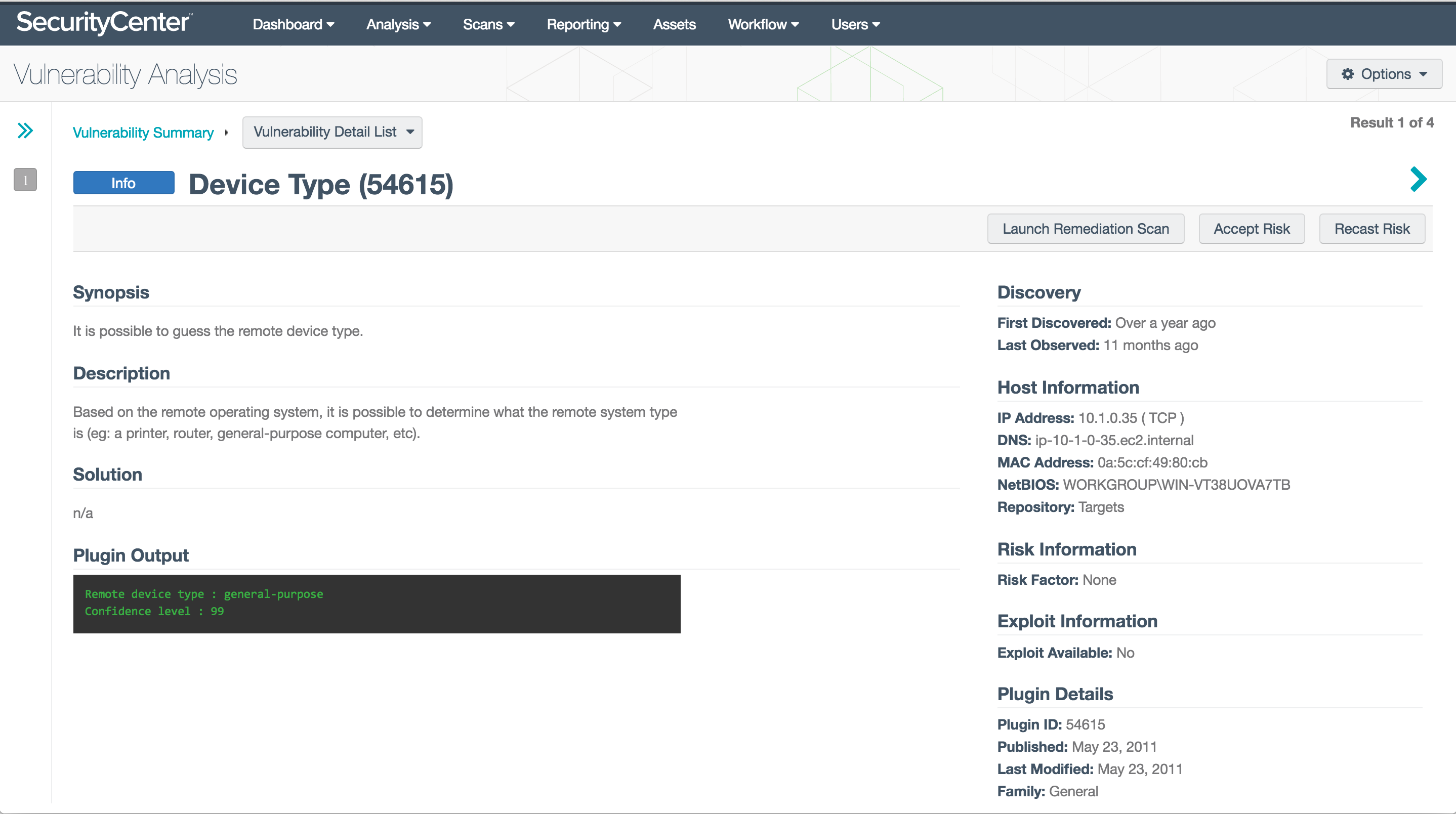
This plugin groups systems into types that you can use to roughly break out what you have on your network:
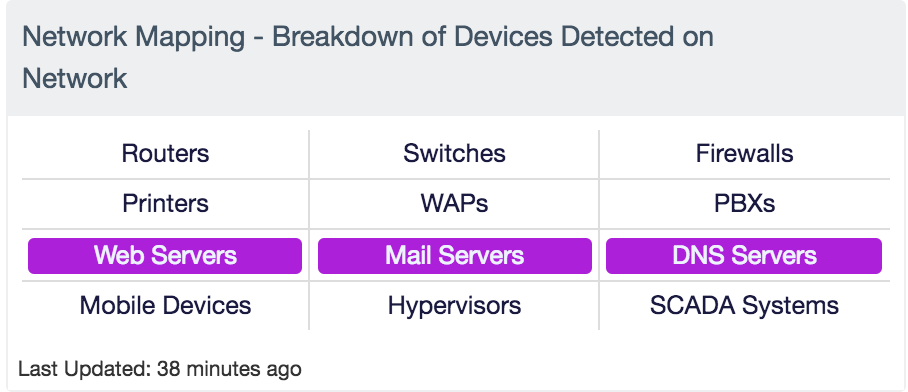
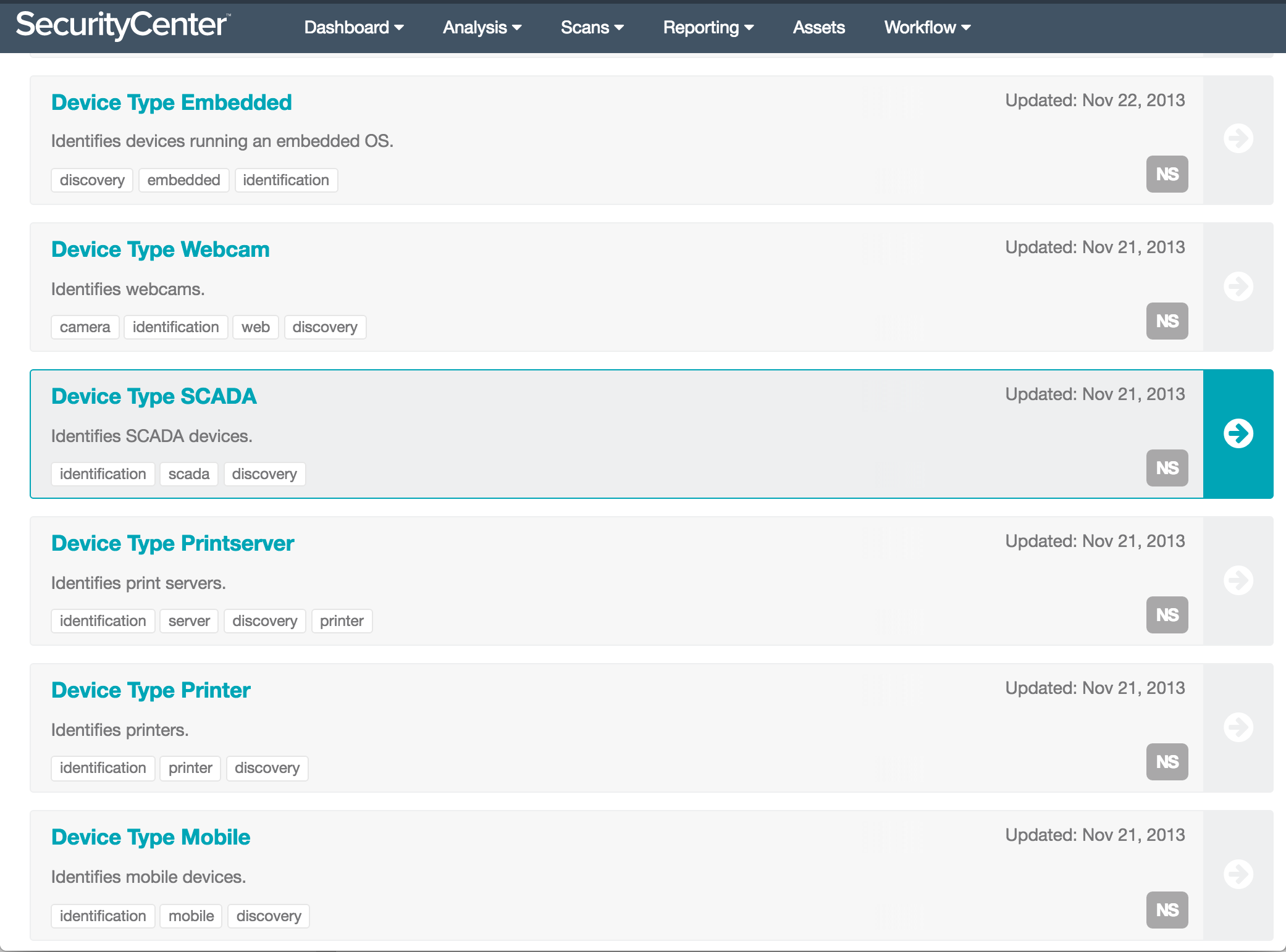
Is there something weird, or infrequent? That’s probably where you should start. The smaller the set of systems you’re working with initially to filter and tune things, the simpler it will be. Some examples of common assets to start with in our library are embedded devices, webcams, SCADA devices, mobile devices and printers:
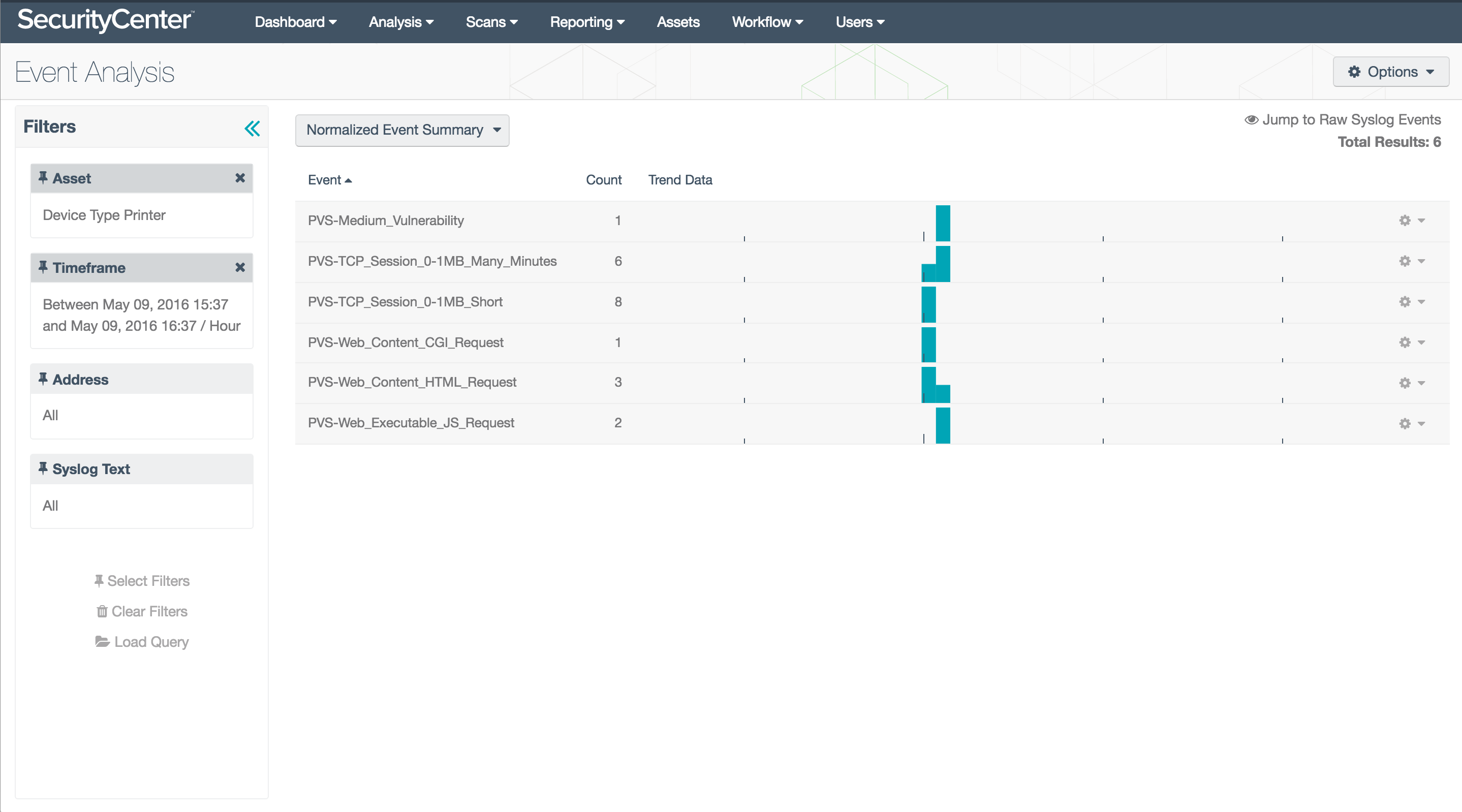
A great example is printers. Generally, they have a specific function on your network. They have a web interface but should not be communicating with the internet. Using an asset list to identify and isolate the activity of your printers lets you see what they’re doing, without the noise of the rest of your environment:
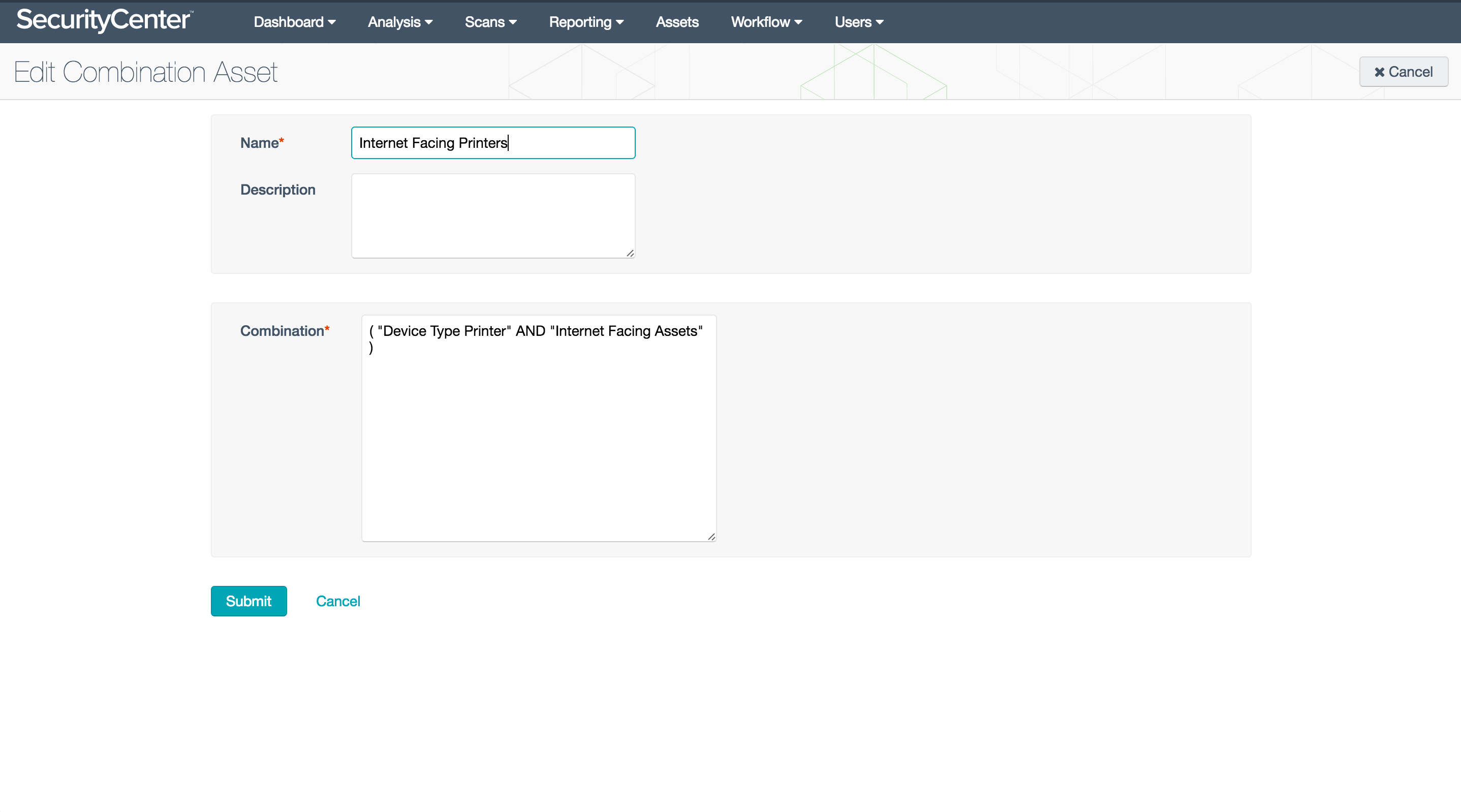
In theory, the activity should seem pretty flat and homogenous. That’s a good thing… You can create filters for those normal things so that the abnormal ones come up more apparently. What ports do they talk on normally, and to whom? Filter out those normal combinations so you can see more clearly. In order to see printers talking with the internet, try using a combination asset list:
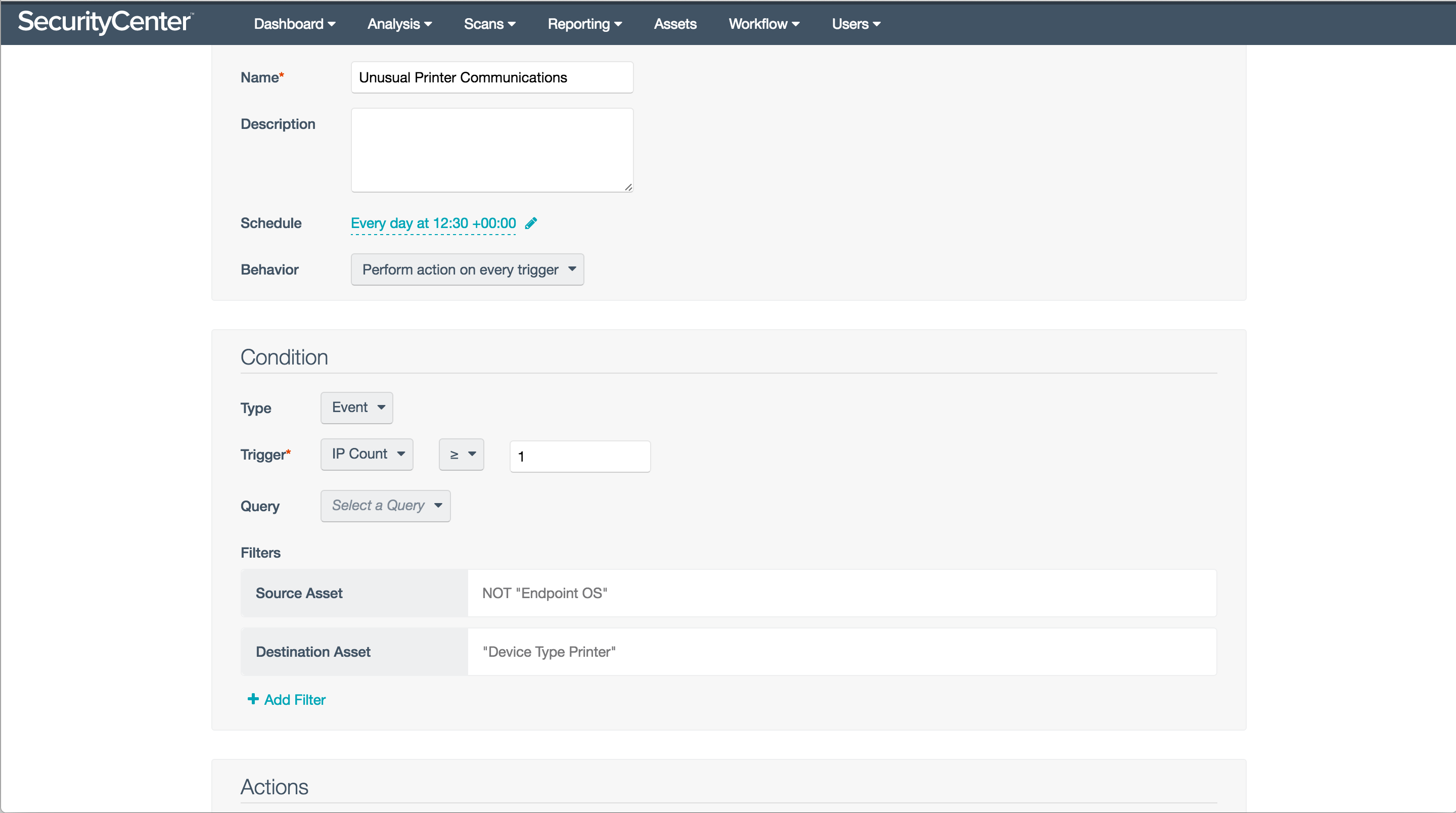
Printer communications are usually very well defined, with endpoints directly talking to printers, or alternatively using a print server to manage jobs. If endpoints are printing directly, it would be unusual for anything else to communicate with printers. We can use asset lists to determine which systems are endpoints; then isolate ones that aren’t endpoints, that are talking to your printers:
Creating alerts for these unusual conditions when they occur is the equivalent of an early warning for a coming storm. SecurityCenter™ will check periodically to determine if any new hosts match the criteria you’ve set up, and will alert in a variety of ways: email, notifications, syslog, etc.
Devices like printers, that have set patterns to their activity, are much easier to monitor for threat activity than dynamic resources. When you’re learning your toolset, they’re a great place to start. Once you’ve classified one device type, move on to another and you’ll gradually get more familiar with your overall exposure, and improve your defenses as well as your detection capabilities.
Visit our website to learn more about Tenable’s Threat Hunting solution and SecurityCenter capabilities.
Related Articles
- Risk-based Vulnerability Management
- SecurityCenter
- Threat hunting
- Threat Intelligence
- Vulnerability Management
- Vulnerability Scanning