Tenable Supports ISO/IEC 27001/27002 and CIS Critical Security Controls

According to the Trends in Security Framework Adoption Survey, research conducted by Dimensional Research on behalf of Tenable, adoption of security frameworks is at an all-time high. Your organization might adopt a security framework for many good reasons, including:
- Identifying security gaps requiring additional investment. Comparing existing security controls to those recommended by an established security framework can highlight weaknesses that require additional controls.
- Communicating business risk to executives and board members. Business leaders are often familiar with financial controls and will quickly grasp the concept of security controls. They will understand budget requests to implement controls needed to mitigate cyber risk.
- Building a foundation to efficiently meet multiple compliance requirements. Rather than tackling each compliance requirement with ad hoc controls, a security framework can provide a single, extensible foundation to meet multiple compliance requirements.
- Discussing security with external stakeholders. Major customers, cyber insurance suppliers and other business partners may have questions about an organization’s security program, and security frameworks provide a structured format for discussion.
- Meeting due care/due diligence standards to limit liability. Many organizations have a legal obligation to understand the cybersecurity risks they face and then to implement appropriate controls that manage that risk. Failure to adequately manage risk may expose the organization, its executives and board members to legal action. For example, a U.S. appeals court recently ruled that the Federal Trade Commission has authority to pursue lawsuits accusing organizations of failing to properly safeguard consumers’ information.
Using multiple frameworks
Many organizations—44% according to the above mentioned survey—are using more than one framework. Some organizations are using a different framework in different parts of their businesses. However, many organizations are using multiple frameworks in a single business area. They are creating their own composite framework based on multiple published frameworks. This makes sense because the Center for Internet Security Critical Security Controls (CSC), ISO/IEC 27001/27002 (ISO 27K) and NIST Framework for Improving Critical Infrastructure Cybersecurity (CSF) frameworks are just that—frameworks. They are not strict standards designed to be adopted without at least some tailoring. The following snippets taken from each standard substantiate this:
- CSF: “The Framework will help the organization align its cybersecurity activities with its business requirements, risk tolerances, and resources,” and “The Framework is adaptive to provide a flexible and risk-based implementation that can be used with a broad array of cybersecurity risk management processes.”
- ISO 27002: “This International Standard may be regarded as a starting point for developing organization-specific guidelines. Not all of the controls and guidance in this code of practice may be applicable.”
- CSC: “But this is not a one-size-fits-all solution, in either content or priority. You must still understand what is critical to your business, data, systems, networks, and infrastructures… ”
Tenable solutions
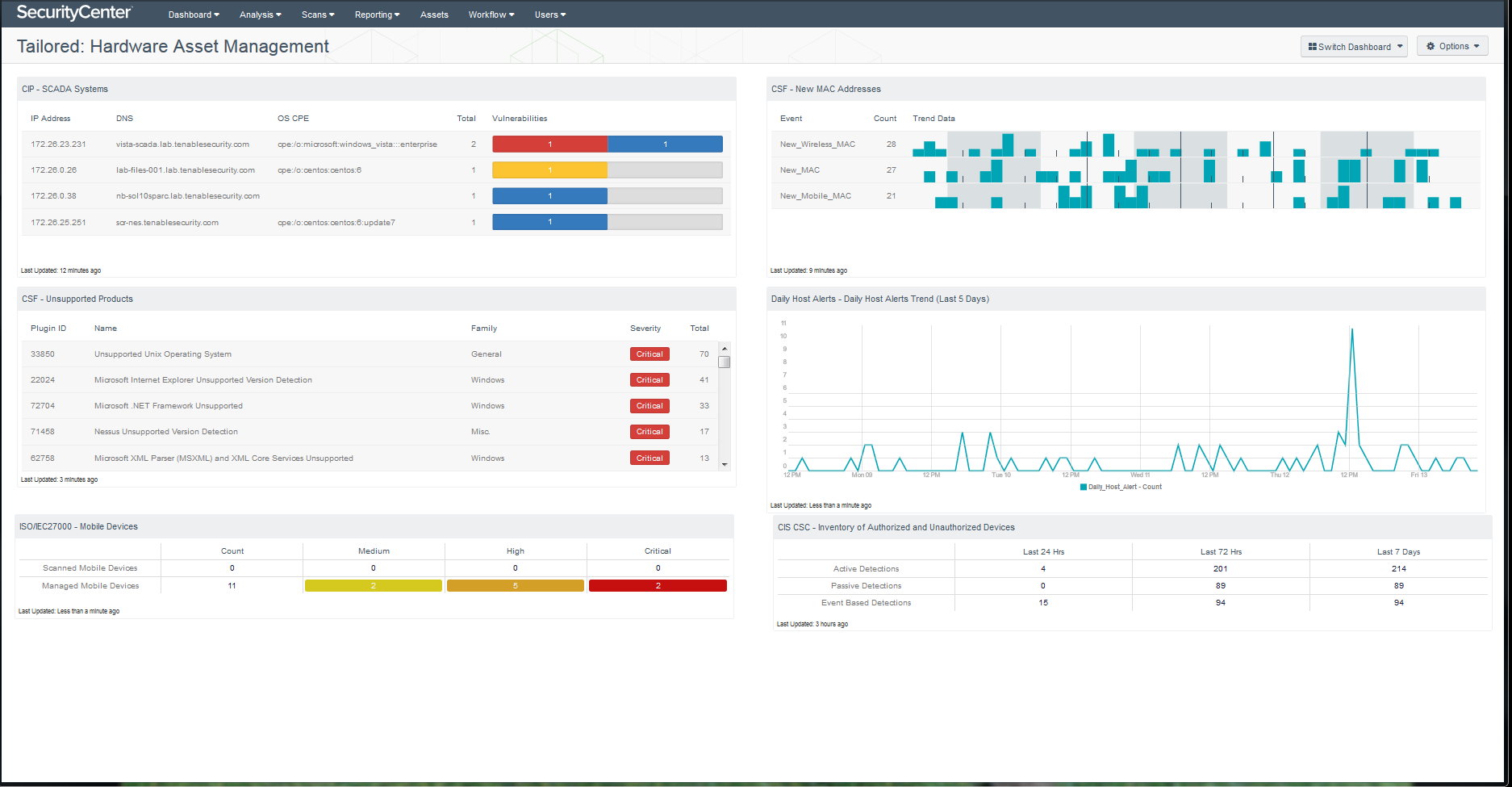
Recognizing the flexibility of these frameworks, Tenable has just released a comprehensive set of report, dashboard and Assurance Report Card (ARC) templates that support ISO 27K and CSC (formerly referred to as the SANS Top 20). You can easily tailor them to meet your specific needs. For example, you can mix and match components designed to support various frameworks, as the dashboard below shows. It includes components initially created for CSF, ISO 27K and CSC frameworks, which you could rename as desired to match your internal language. Additionally, you could easily design your own dashboards leveraging a template or by starting from scratch.
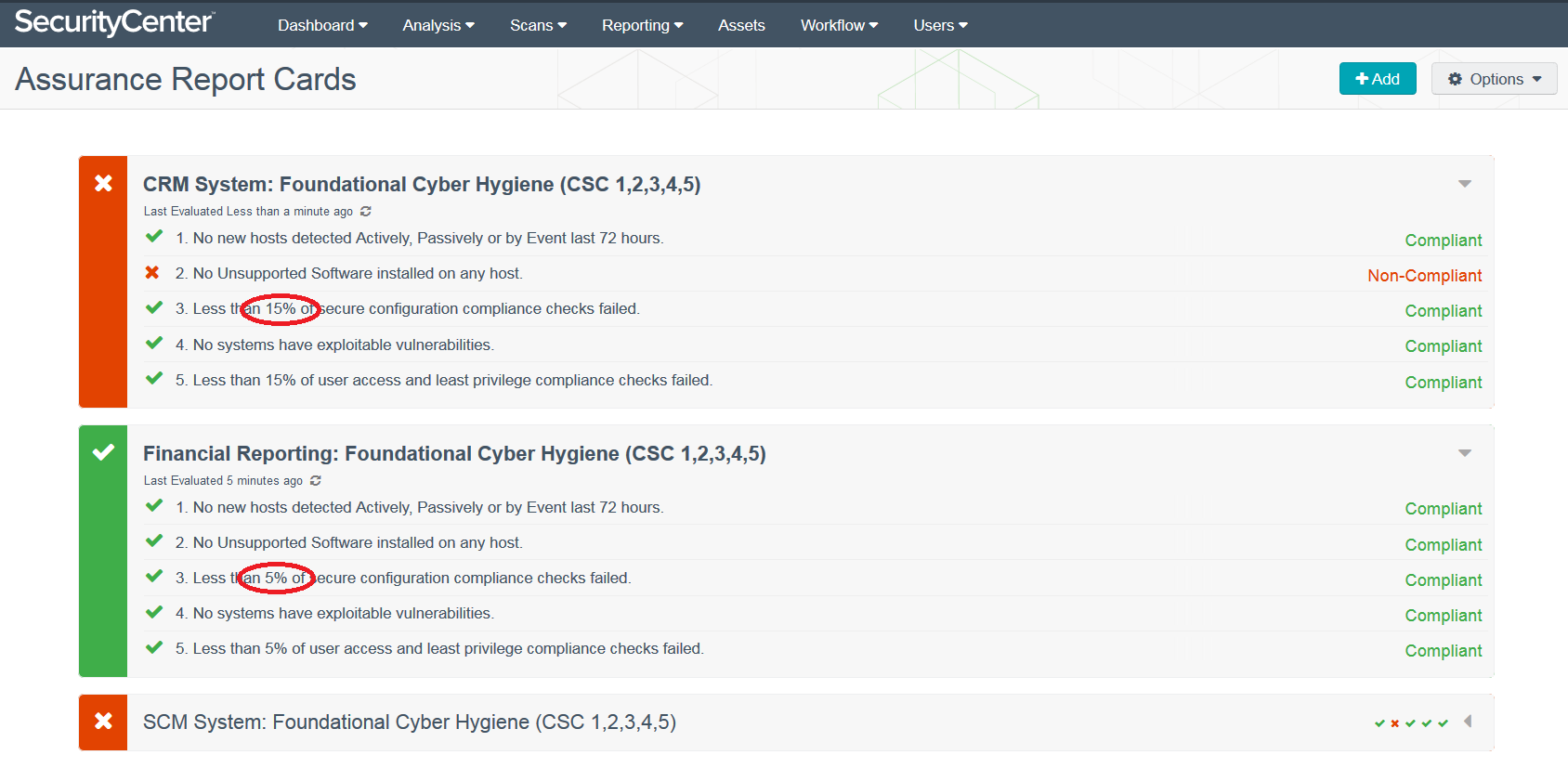
In addition to customizing reports, dashboards and ARCs, you can apply dynamic asset lists to reuse a single template with assets for different business systems. This is especially useful with ARCs because you can set different pass/fail thresholds for different business systems as needed to mitigate different risk levels. The following example displays the status of three different business systems relative to the CSC Foundational Cyber Hygiene controls. Notice the different thresholds for the CRM system and the financial reporting system.
More information
If your organization is using one or more security frameworks, Tenable can help you automate your technical controls and help you assess and communicate their status. Please visit the following pages for additional information:
Keep up with the latest from Tenable! Subscribe to the Tenable Blog by clicking Blog email updates on the Blog Home Page.
Learn more
- Center for Internet Security (CIS)
- ISO
- NIST
- Security Frameworks




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success