Oracle April 2022 Critical Patch Update Addresses 221 CVEs
Oracle addresses 221 CVEs in its second quarterly update of 2022 with 520 patches, including 27 critical updates.
Background
On April 19, Oracle released its Critical Patch Update (CPU) for April 2022, the second quarterly update of the year. This CPU contains fixes for 221 CVEs in 520 security updates across 31 Oracle product families. Out of the 520 security updates published this quarter, 14.8% of patches were assigned critical severity. Medium severity patches accounted for the bulk of the release at 55.2%, followed by high severity patches at 27.1%.
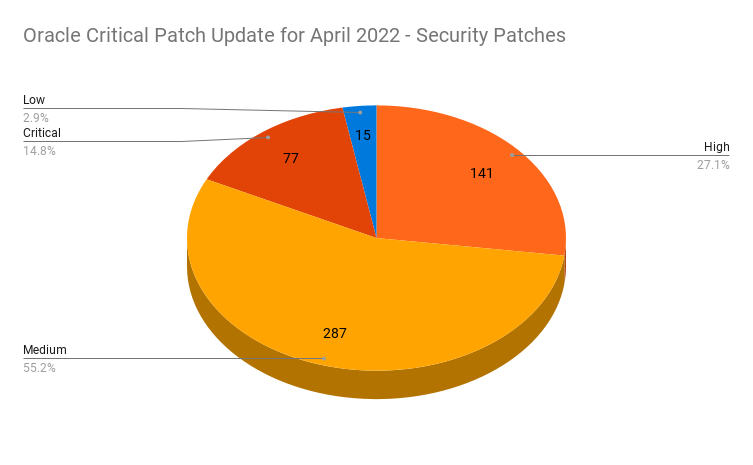
This quarter’s update includes 77 critical patches across 27 CVEs.
| Severity | Issues Patched | CVEs |
|---|---|---|
| Critical | 77 | 27 |
| High | 141 | 69 |
| Medium | 287 | 114 |
| Low | 15 | 11 |
| Total | 520 | 221 |
Analysis
This quarter, the Oracle Communications product family contained the highest number of patches at 149, accounting for 28.6% of the total patches, followed by Oracle Fusion Middleware at 54 patches, which accounted for 10.4% of the total patches.
Two CVEs receive the highest possible CVSS Score
This month's CPU release included two CVEs that were given a CVSSv3 score of 10.0, the highest possible severity.
CVE-2022-22947 is a vulnerability impacting the Oracle Communications product family that can be exploited by an unauthenticated attacker with network access via HTTP. This vulnerability would allow a remote attacker to exploit arbitrary code when the Spring Cloud gateway actuator is enabled and unsecured.
CVE-2022-21431 is a vulnerability in the Connection Manager component of the Oracle Communications Billing and Revenue Management product that can be exploited by an unauthenticated attacker with network access via TCP to gain full control of the Billing and Revenue Management service; however, Oracle indicates that exploitation of this vulnerability could “significantly impact additional products.”
Oracle addresses “psychic signatures” vulnerability in Java
Additionally, Oracle addressed CVE-2022-21449, a cryptographic signature vulnerability in Java 15, 16, 17 and 18. It has been referred to as a “psychic signatures” vulnerability by Neil Madden, security architect at Forgerock, who published a detailed blog post about the flaw. While Oracle assigned a CVSSv3 score of 7.5 to the vulnerability, Madden says that Forgerock assigned a CVSSv3 score of 10.0.
Three product families receive only third party patches
While 31 product families received security patches this quarter, Oracle did not include security patches for three product families:
- Oracle Global Lifecycle Management
- Oracle NoSQL Database
- Oracle Secure Backup
While these three product families did not receive security patches, Oracle notes that there are third-party patches included as part of its CPU release:
| Oracle Product Family | Component | CVE |
|---|---|---|
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-37137 |
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-21290 |
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-21295 |
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-21409 |
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-30129 |
| Oracle NoSQL Database | Administration (Netty) | CVE-2021-37136 |
| Oracle NoSQL Database | Administration (Apache MINA SSHD) | CVE-2021-30129 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-44790 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-32785 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-32786 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-32791 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-32792 |
| Oracle Secure Backup | Secure Backup (Apache HTTP Server) | CVE-2021-44224 |
| Oracle Secure Backup | Secure Backup (PHP) | CVE-2021-21703 |
| Oracle Global Lifecycle Management OPatch | Centralized Third Party Jars (Apache Commons Compress) | CVE-2021-36090 |
| Oracle Global Lifecycle Management OPatch | Centralized Third Party Jars (Apache Commons Compress) | CVE-2021-35515 |
| Oracle Global Lifecycle Management OPatch | Centralized Third Party Jars (Apache Commons Compress) | CVE-2021-35516 |
| Oracle Global Lifecycle Management OPatch | Centralized Third Party Jars (Apache Commons Compress) | CVE-2021-35517 |
Third party patches also include fixes for Apache Log4j
Oracle has also addressed multiple additional third party patches in this release, including fixes for vulnerabilities in Apache Log4j, most notably a remote code execution vulnerability dubbed Log4Shell and originally disclosed in December.
| Third Party Component | CVE |
|---|---|
| Apache Tomcat | CVE-2021-42340 |
| Apache Log4j | CVE-2021-44832 |
| Apache Log4j | CVE-2022-23305 |
| Apache Xerces-J | CVE-2022-23437 |
| Apache Kafka | CVE-2021-38153 |
| Jakarta | CVE-2021-28170 |
| Guava | CVE-2020-8908 |
A full breakdown of the patches for this quarter can be seen in the following table, which also includes a count of vulnerabilities that can be exploited over a network without authentication.
| Oracle Product Family | Number of Patches | Remote Exploit without Auth |
|---|---|---|
| Oracle Communications | 149 | 98 |
| Oracle Fusion Middleware | 54 | 41 |
| Oracle MySQL | 43 | 11 |
| Oracle Financial Services Applications | 41 | 19 |
| Oracle Communications Applications | 39 | 22 |
| Oracle Retail Applications | 30 | 15 |
| Oracle Systems | 20 | 14 |
| Oracle Blockchain Platform | 15 | 14 |
| Oracle PeopleSoft | 14 | 8 |
| Oracle Hyperion | 12 | 4 |
| Oracle Supply Chain | 11 | 5 |
| Oracle Enterprise Manager | 10 | 7 |
| Oracle HealthCare Applications | 10 | 5 |
| Oracle JD Edwards | 8 | 8 |
| Oracle Commerce | 7 | 3 |
| Oracle Insurance Applications | 7 | 5 |
| Oracle Java SE | 7 | 7 |
| Oracle Hospitality Applications | 6 | 2 |
| Oracle Virtualization | 6 | 1 |
| Oracle Database Server | 5 | 0 |
| Oracle GoldenGate | 5 | 4 |
| Oracle E-Business Suite | 5 | 2 |
| Oracle Construction and Engineering | 3 | 1 |
| Oracle Health Sciences Applications | 3 | 1 |
| Oracle Support Tools | 3 | 1 |
| Oracle SQL Developer | 2 | 1 |
| Oracle Autonomous Health Framework | 1 | 0 |
| Oracle REST Data Services | 1 | 0 |
| Oracle iLearning | 1 | 1 |
| Oracle Taleo | 1 | 0 |
| Oracle Utilities Applications | 1 | 0 |
Solution
Customers are advised to apply all relevant patches in this quarter’s CPU. Please refer to the April 2022 advisory for full details.
Identifying affected systems
A list of Tenable plugins to identify these vulnerabilities will appear here as they’re released.
Get more information
- Oracle Critical Patch Update Advisory - April 2022
- Oracle April 2022 Critical Patch Update Risk Matrices
- Oracle Advisory to CVE Map
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management


Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success