Colonial Pipeline Ransomware Attack: How to Reduce Risk in OT Environments
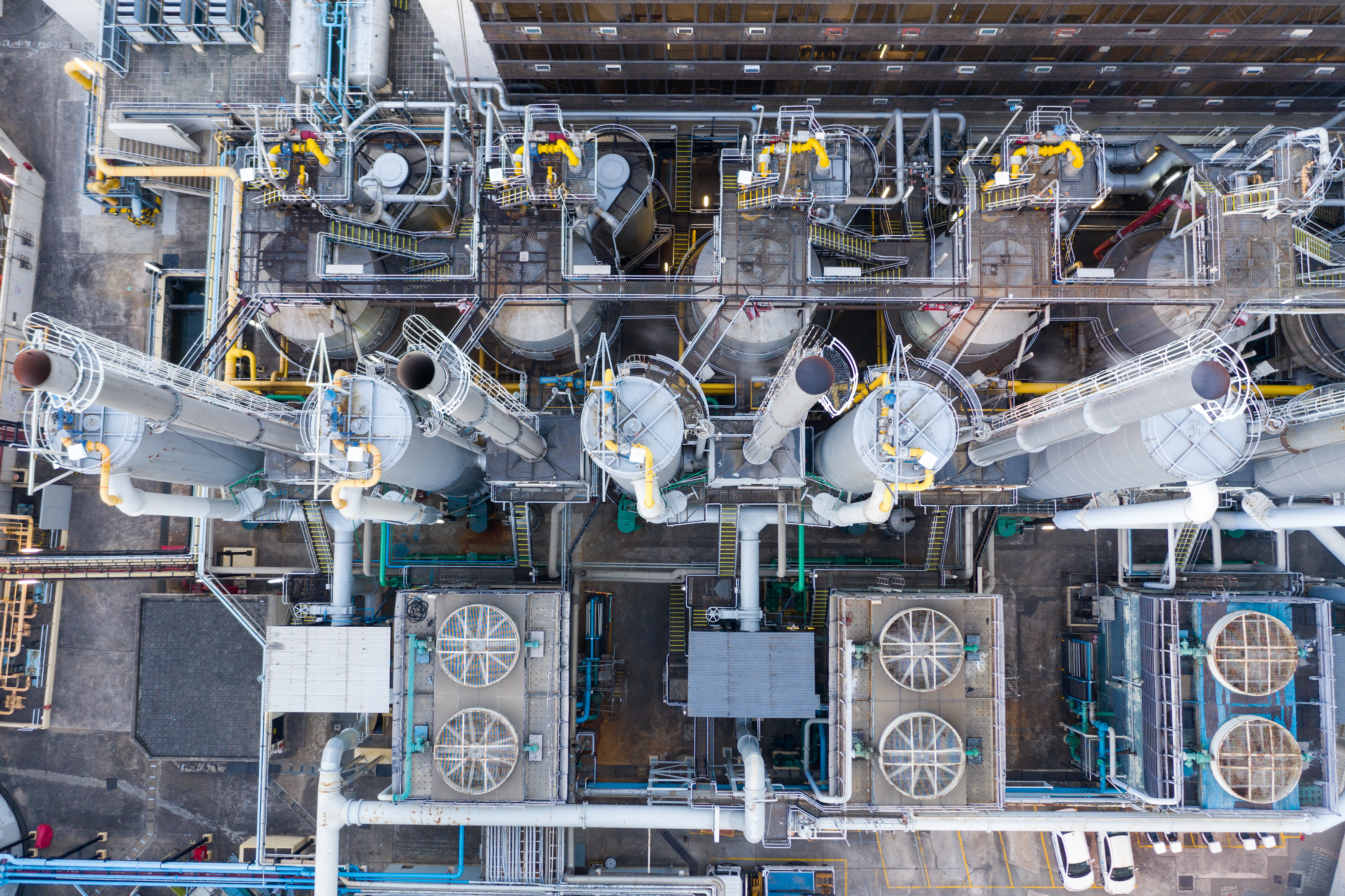
It's time for Operational Technology (OT) environments to pursue a more proactive approach to cybersecurity by making cyber maintenance as much of a routine practice as the mechanical maintenance of systems and equipment.
A major supplier of oil and gas to the U.S. East Coast was taken offline on May 8 after a reported ransomware attack. The attack on the 5,500 mile Colonial Pipeline, which supplies 45 percent of the oil and gas used on the East Coast, is just the latest to target the oil and gas sector, which is considered one of 16 critical infrastructure areas identified by the U.S. Department of Homeland Security
It is not surprising that a shutdown or interruption of a pipeline would gain major media attention. But the attack also begs the question: how exposed to attacks is our critical infrastructure?
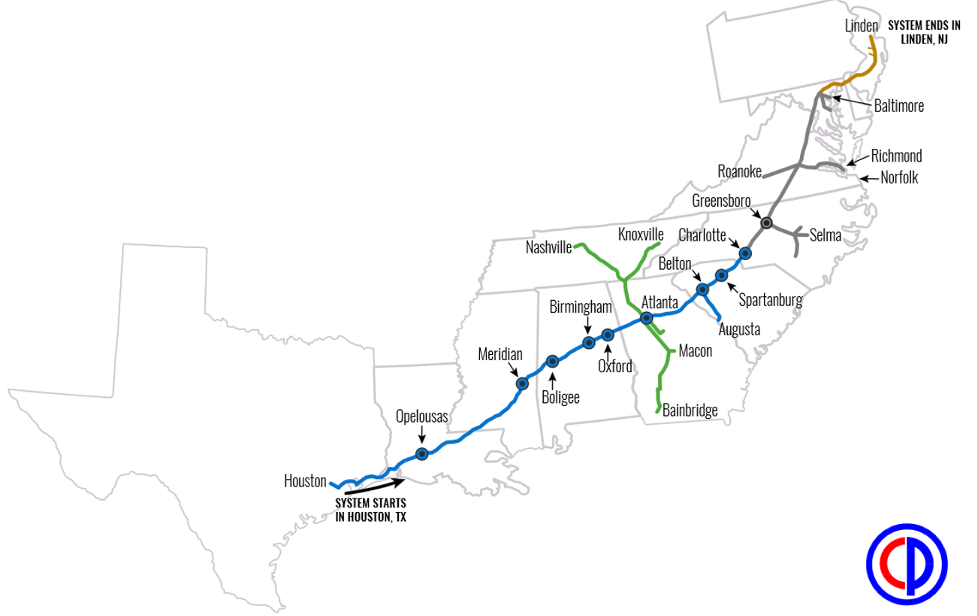
Source: Colonial Pipeline
The changing operating technology paradigm
While the operational technology (OT) required in oil and gas operations was once isolated and "air-gapped," today these systems are increasingly connected to IT infrastructure and to the internet, opening up new attack paths. This convergence creates an environment in which any and all aspects of oil and gas operations could be vulnerable to attack from either the IT or the OT side, opening up the possibility of lateral movement.
Additionally, many ransomware attacks use Active Directory (AD) to perform lateral movement and privilege escalation after initial penetration and new malware increasingly includes codes to target AD misconfigurations. AD has become the favored target for attackers to elevate privileges and facilitate lateral movement through leveraging known flaws and misconfigurations. Unfortunately, most organizations struggle with Active Directory security due to misconfigurations piling up as domains increase in complexity, leaving security teams unable to find and fix flaws before they become business-impacting issues.
The attack against Colonial Pipeline is just the latest in a series of recent activity against oil and gas operations around the globe, including:
- Saipem, an Italian oil and gas industry contractor, which fell victim to a December 2018 cyberattack hitting servers based in the Middle East, India, Aberdeen and Italy.
- A cyberattack on a shared data network, which forced four natural gas pipeline operators in the U.S. to temporarily shut down computer communications with their customers in April 2018.
- A cyberattack against a U.S. natural gas facility, which concurrently encrypted both the IT and OT networks, locking access to the human machine interface (HMI), data historians and polling servers. The pipeline was forced to shut down for two days in February 2020.
Regulatory compliance does not equal security
In our experience working with OT environments, we often find organizations assuming that regulatory compliance is the same as security. While we are by no means suggesting this was the case at Colonial Pipeline, we do believe it's worthwhile for all organizations in the sector to consider taking a more expansive view of their cybersecurity strategy.
There are five safety and security standards relevant to the oil and gas industry, all of which call for organizations to have a base layer of security in place. This layer includes asset inventory, security management controls and a vulnerability management system. While we support a regulatory approach and believe compliance is laudable, we consider adherence to these guidelines as only the beginning of a sound cybersecurity strategy.
Here's why: the promulgation, enactment and enforcement of regulatory standards cannot keep pace with the rapidly expanding attack surface, and the speed with which attackers adapt to it. Thus, we cannot assume "compliance" means the organization has achieved "security." We must look well beyond compliance if we hope to keep critical infrastructure secure and prevent attacks like the one that has affected Colonial Pipeline.
5 safety and security standards relevant to the oil and gas industry
API Standard 1164 - Content unique to pipelines not covered by NIST CSF and IEC 62443.
National Institute of Standards and Technology (NIST) cybersecurity framework for improving critical infrastructure cybersecurity (NIST CSF) - Pre-eminent framework adopted by companies in all industry sectors; Natural gas and oil companies increasingly orient enterprisewide programs around NIST CSF.
Department of Energy cybersecurity capability maturity model - Voluntary process using industry-accepted best practices to measure the maturity of an organization's cybersecurity capabilities and strengthen operations.
International Electrotechnical Commission (IEC) 62443 - Family of standards for industrial control systems (ICS) security; widely adopted by production segment of natural gas and oil industry; applicable to any type of natural gas and oil ICS
International Organization for Standardization ISO 27000 - Leading standard in the family providing requirements for an information security management system (ISMS).
How to disrupt OT security threats
Ironically, one of the least desirable times to deal with a cyberattack is when it is happening. Over the coming days and weeks, we will undoubtedly learn more details about the course of this attack, as well as the cost and disruption it caused. If critical infrastructure organizations have any hope of getting out of the cyber firefighting mode of having to react to attacks, they will need to instead focus on preempting attacks by disrupting them before they happen.
Many industrial environments, including the oil and gas industry, are very familiar with performing routine maintenance on their equipment. Whether it is changing out a bearing, filter or fluids, maintenance is performed to avoid a catastrophic equipment failure due to what's known as "running to failure." Regular maintenance saves money and aggravation and avoids the diversion of resources.
So, why aren't organizations performing the same type of regular maintenance on the cybersecurity of their OT systems?
Taking a "maintenance" approach to OT infrastructure means performing the appropriate cyber hygiene on the programmable logic controllers (PLCs), distributed control systems (DCSs), HMIs and other OT devices that run these machines. Performing regular cyber hygiene can reduce OT threats by stopping risky behavior, closing "ports of entry" and reducing the amount of vulnerabilities that can be exploited.
Reducing threats before they happen requires:
- achieving visibility across the entire attack surface — including IT and OT systems;
- deploying deep security measures at the device and network level; and
- re-establishing control through managing configuration changes.
Organizations need appropriate cyber hygiene in both their OT infrastructure and their Active Directory to reduce their cyber exposure and ensure that attack paths are cut off before attackers can succeed in escalating privileges, traversing the network and launching their ransomware attempt. These efforts can help all critical infrastructure and manufacturing operations avoid having to respond to a security crisis that can stop operations and potentially put human lives at risk.
Learn More
- Download the whitepaper: Critical Infrastructure Cybersecurity
- View our on-demand webinar: Critical Infrastructure at Risk: Anatomy of an OT Breach
Learn more
- Energy Industry
- Federal
- Government
- Incident Response
- OT Security
- Standards
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success