by Cody Dumont
March 8, 2016
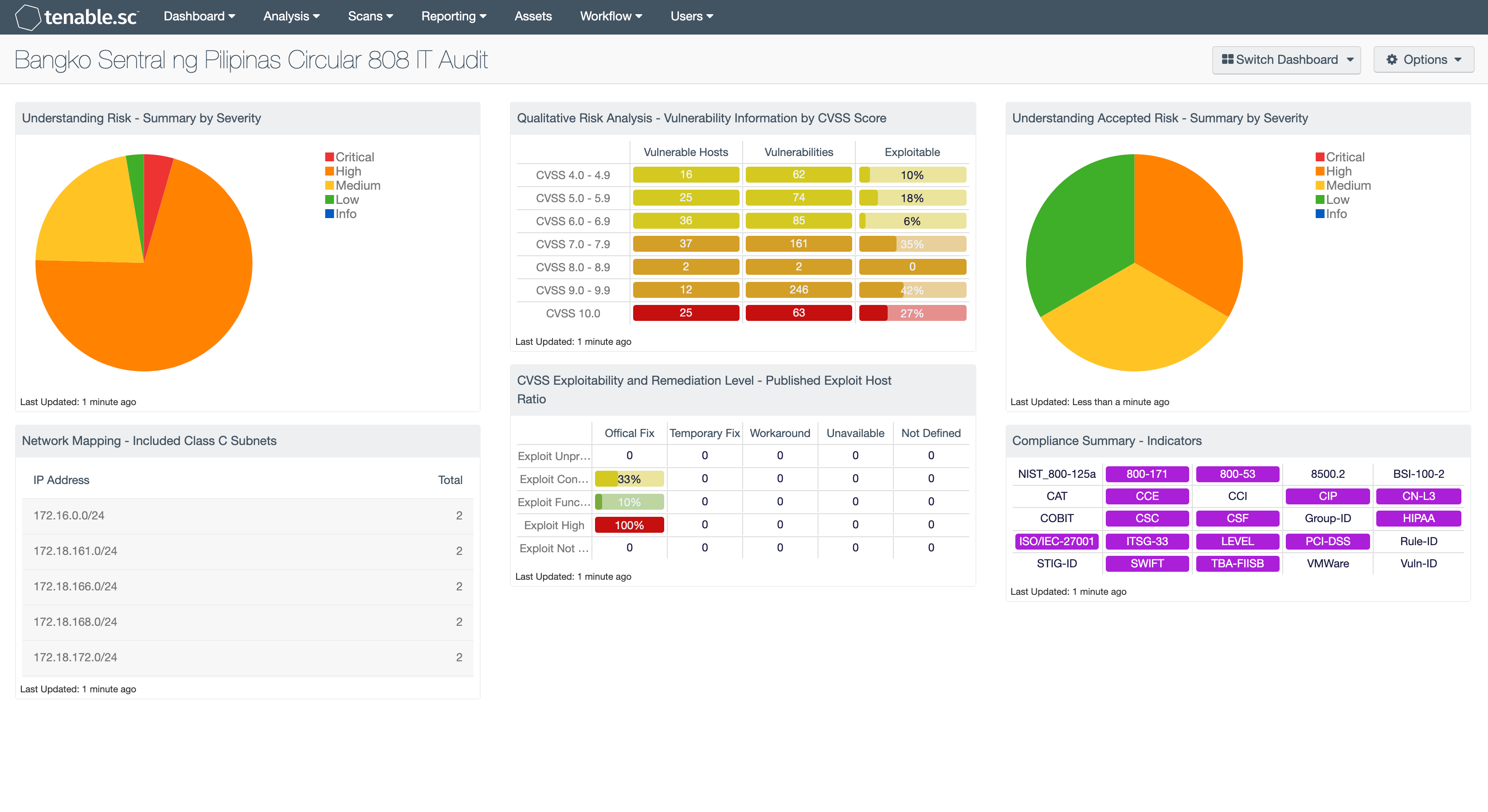
Information Technology Risk Management is crucial for any financial institution to protect their critical assets from potential cyber attacks. The Bangko Sentral ng Pilipinas (BSP) Circular 808 (August 2013) provides guidelines to assist the BSP Supervised Institutions (BSI) with the adoption of technology in the financial service industry. The dashboard focuses on Appendix 75a IT Audit.
As the growing number of BSIs deploy innovative technologies to reduce risk, the need to properly monitor and audit these technologies increases. BSIs need to ensure the environment is properly audited to identify deficiencies in security controls and IT operations. The IT Audit Area defines the requirements to create plans to manage and monitor rapidly changing technologies. The IT Audit scope is not limited to system configurations, but also includes IT operations, strategic planning, and physical security controls. Tenable.sc Continuous View (CV) can be used to analyze and report on client/server architecture, network communications, and telecommunications. The scalability of Tenable.sc CV allows for regular assessments for vulnerabilities and against established configuration standards.
As the vulnerability and audit data is collected, Tenable.sc CV can also assist with quantitative analysis by supporting CVSS scores and qualitative using the CVSS vector codes. Both assist the IT audit team in performing a proper risk analysis.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.2.0
- Nessus 8.5.1
- Compliance Scan Results
Tenable.sc Continuous View (CW) provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. When implementing Tenable.sc CV with Nessus, Log Correlation Engine (LCE), and the Nessus Network Monitor (NNM), Tenable is able to provide the most comprehensive and integrated view of network health. Tenable.sc CV provides peace of mind to customers by: detecting security and compliance issues before our competitors, proactively identifying the biggest risk in the enterprise network, and enabling the BSI to react to advanced threats, zero-day vulnerabilities, and new forms of regulatory compliance.
Components
Understanding Risk - Summary by Severity: In paragraph 5.2 there is discussion about how risk is to be assessed. This component provides an over all view of risk by severity. The objective is to have informational and low severities; if this is not the case, then IT operations may not be mitigating risk as directed.
Network Mapping - Included Class C Subnets: In paragraph 4.1 there is a list outlining the requirements for an audit program. This component helps to identify all the assets that can be assessed by Tenable.sc CV.
Qualitative Risk Analysis - Vulnerability Information by CVSS Score: In paragraph 5.2 there is discussion about how risk is to be measured that can help rank and evaluate business risk. CVSS scoring is an international method of assigning quantitative values to known vulnerabilities.
OWASP Top 10 - Web App Result Indicator: In paragraph 5.2 there is discussion about how to monitor risk in applications. OWASP is an open source project used to measure risk to web applications.
CVSS Exploitability and Remediation Level - Published Exploit Host Ratio: In paragraph 5.2 there is discussion about how risk is to be measured that can help rank and evaluate business risk. CVSS vector coding is an international method of assigning qualitative values to known vulnerabilities.
Understanding Accepted Risk - Summary by Severity: In paragraph 5.2 there is discussion about risk assessment. This component provides a high level view of risks that have been accepted.
Compliance Summary – Indicators: In paragraph 4.1 there is discussion on selecting standards for system configurations. This component provides a high level overview of audits that have been completed against all supported standards.